Category: Uncategorized
-
Qilin Ransomware Adds “Call Lawyer” Feature to Pressure Victims for Larger Ransoms [email protected] (The Hacker News)
The threat actors behind the Qilin ransomware-as-a-service (RaaS) scheme are now offering legal counsel for affiliates to put more pressure on victims to pay up, as the cybercrime group intensifies its activity and tries to fill the void left by its rivals. The new feature takes the form of a “Call Lawyer” feature on the…
-
News brief: LOTL attacks, spoofed sites, malicious repositories
Check out the latest security news from the Informa TechTarget team.Read More
-

Iran’s State TV Hijacked Mid-Broadcast Amid Geopolitical Tensions; $90M Stolen in Crypto Heist [email protected] (The Hacker News)
Iran’s state-owned TV broadcaster was hacked Wednesday night to interrupt regular programming and air videos calling for street protests against the Iranian government, according to multiple reports. It’s currently not known who is behind the attack, although Iran pointed fingers at Israel, per Iran International. “If you experience disruptions or irrelevant messages while watching various…
-

6 Steps to 24/7 In-House SOC Success [email protected] (The Hacker News)
Hackers never sleep, so why should enterprise defenses? Threat actors prefer to target businesses during off-hours. That’s when they can count on fewer security personnel monitoring systems, delaying response and remediation. When retail giant Marks & Spencer experienced a security event over Easter weekend, they were forced to shut down their online operations, which account…
-
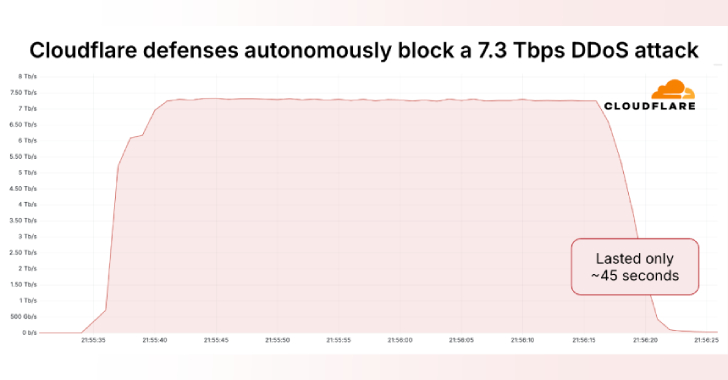
Massive 7.3 Tbps DDoS Attack Delivers 37.4 TB in 45 Seconds, Targeting Hosting Provider [email protected] (The Hacker News)
Cloudflare on Thursday said it autonomously blocked the largest ever distributed denial-of-service (DDoS) attack ever recorded, which hit a peak of 7.3 terabits per second (Tbps). The attack, which was detected in mid-May 2025, targeted an unnamed hosting provider. “Hosting providers and critical Internet infrastructure have increasingly become targets of DDoS attacks,” Cloudflare’s OmerRead More
-

67 Trojanized GitHub Repositories Found in Campaign Targeting Gamers and Developers [email protected] (The Hacker News)
Cybersecurity researchers have uncovered a new campaign in which the threat actors have published more than 67 GitHub repositories that claim to offer Python-based hacking tools, but deliver trojanized payloads instead. The activity, codenamed Banana Squad by ReversingLabs, is assessed to be a continuation of a rogue Python campaign that was identified in 2023 as…
-
What is risk assessment?
Risk assessment is the process of identifying hazards that could negatively affect an organization’s ability to conduct business.Read More
-

New Android Malware Surge Hits Devices via Overlays, Virtualization Fraud and NFC Theft [email protected] (The Hacker News)
Cybersecurity researchers have exposed the inner workings of an Android malware called AntiDot that has compromised over 3,775 devices as part of 273 unique campaigns. “Operated by the financially motivated threat actor LARVA-398, AntiDot is actively sold as a Malware-as-a-Service (MaaS) on underground forums and has been linked to a wide range of mobile campaigns,”…
-

BlueNoroff Deepfake Zoom Scam Hits Crypto Employee with MacOS Backdoor Malware [email protected] (The Hacker News)
The North Korea-aligned threat actor known as BlueNoroff has been observed targeting an employee in the Web3 sector with deceptive Zoom calls featuring deepfaked company executives to trick them into installing malware on their Apple macOS devices. Huntress, which revealed details of the cyber intrusion, said the attack targeted an unnamed cryptocurrency foundation employee, who…
-

Secure Vibe Coding: The Complete New Guide [email protected] (The Hacker News)
DALL-E for coders? That’s the promise behind vibe coding, a term describing the use of natural language to create software. While this ushers in a new era of AI-generated code, it introduces “silent killer” vulnerabilities: exploitable flaws that evade traditional security tools despite perfect test performance. A detailed analysis of secure vibe coding practices is…
