“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-

UAC-0063 Expands Cyber Attacks to European Embassies Using Stolen Documents [email protected] (The Hacker News)
The advanced persistent threat (APT) group known as UAC-0063 has been observed leveraging legitimate documents obtained by infiltrating one victim to attack another target with the goal of delivering a known malware dubbed HATVIBE. “This research focuses on completing the picture of UAC-0063’s operations, particularly documenting their expansion beyond their initial focus on Central Asia,Read…
-
Broadcom Warns of High-Severity SQL Injection Flaw in VMware Avi Load Balancer [email protected] (The Hacker News)
Broadcom has alerted of a high-severity security flaw in VMware Avi Load Balancer that could be weaponized by malicious actors to gain entrenched database access. The vulnerability, tracked as CVE-2025-22217 (CVSS score: 8.6), has been described as an unauthenticated blind SQL injection. “A malicious user with network access may be able to use specially crafted…
-

Zyxel CPE Devices Face Active Exploitation Due to Unpatched CVE-2024-40891 Vulnerability [email protected] (The Hacker News)
Cybersecurity researchers are warning that a critical zero-day vulnerability impacting Zyxel CPE Series devices is seeing active exploitation attempts in the wild. “Attackers can leverage this vulnerability to execute arbitrary commands on affected devices, leading to complete system compromise, data exfiltration, or network infiltration,” GreyNoise researcher Glenn Thorpe said in an alertRead More
-
PureCrypter Deploys Agent Tesla and New TorNet Backdoor in Ongoing Cyberattacks [email protected] (The Hacker News)
A financially motivated threat actor has been linked to an ongoing phishing email campaign that has been ongoing since at least July 2024 specifically targeting users in Poland and Germany. The attacks have led to the deployment of various payloads, such as Agent Tesla, Snake Keylogger, and a previously undocumented backdoor dubbed TorNet that’s delivered…
-
DeepSeek claims ‘malicious attacks’ disrupting AI service
Post ContentRead More
-

OAuth Redirect Flaw in Airline Travel Integration Exposes Millions to Account Hijacking [email protected] (The Hacker News)
Cybersecurity researchers have disclosed details of a now-patched account takeover vulnerability affecting a popular online travel service for hotel and car rentals. “By exploiting this flaw, attackers can gain unauthorized access to any user’s account within the system, effectively allowing them to impersonate the victim and perform an array of actions on their behalf –…
-
Apple zero-day vulnerability under attack on iOS devices
Post ContentRead More
-

AI SOC Analysts: Propelling SecOps into the future [email protected] (The Hacker News)
Triaging and investigating alerts is central to security operations. As SOC teams strive to keep up with ever-increasing alert volumes and complexity, modernizing SOC automation strategies with AI has emerged as a critical solution. This blog explores how an AI SOC Analyst transforms alert management, addressing key SOC challenges while enabling faster investigations and responses.…
-

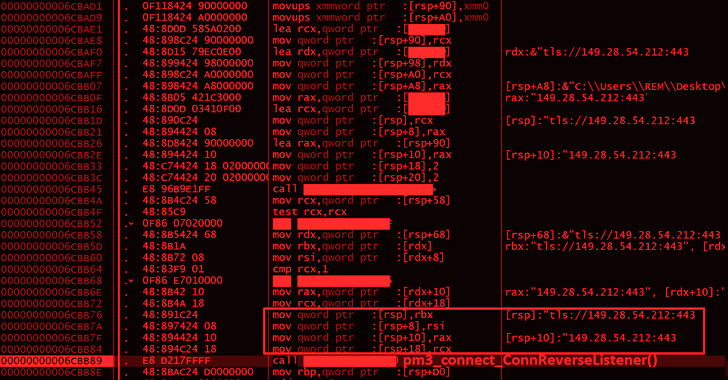
Ransomware Targets ESXi Systems via Stealthy SSH Tunnels for C2 Operations [email protected] (The Hacker News)
Cybersecurity researchers have found that ransomware attacks targeting ESXi systems are also leveraging the access to repurpose the appliances as a conduit to tunnel traffic to command-and-control (C2) infrastructure and stay under the radar. “ESXi appliances, which are unmonitored, are increasingly exploited as a persistence mechanism and gateway to access corporate networks widely,” SygniaRead More
-

How Long Does It Take Hackers to Crack Modern Hashing Algorithms? [email protected] (The Hacker News)
While passwords remain the first line of defense for protecting user accounts against unauthorized access, the methods for creating strong passwords and protecting them are continually evolving. For example, NIST password recommendations are now prioritizing password length over complexity. Hashing, however, remains a non-negotiable. Even long secure passphrases should be hashed to prevent themRead More
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
