“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-
New HTTP/2 Bomb Vulnerability Allows Remote DoS on NGINX, Apache, IIS, Envoy & Cloudflare [email protected] (The Hacker News)
Cybersecurity researchers have discovered a remote denial-of-service exploit that affects major web servers, including NGINX, Apache HTTPD, Microsoft IIS, Envoy, and Cloudflare Pingora. The vulnerability has been codenamed HTTP/2 Bomb by Calif. “The vulnerable behavior exists in each server’s default HTTP/2 configuration,” the company said, adding it was discovered by OpenAI Codex by chainingRead More
-
Weedhack Attacks Minecraft Users, CountLoader Hits 86K, Miners Spread via Pirated Content [email protected] (The Hacker News)
Cybersecurity researchers have flagged a new campaign targeting Minecraft players via YouTube to spread malware capable of gaining control of victims’ systems. The Minecraft-focused malware-as-a-service (MaaS) campaign has been codenamed Weedhack by McAfee Labs, stating the activity has been active since January 2026 and impersonates Minecraft clients and mods to infect users. In all, 3820Read…
-

Google June 2026 Android Update Patches 124 Flaws, One Actively Exploited [email protected] (The Hacker News)
Google on Monday released patches for 124 security vulnerabilities impacting its Android operating system for the month of June 2026, including one high-severity flaw in the Framework component that has come under active exploitation. Tracked as CVE-2025-48595 (CVSS score: 8.4), the security flaw has been described as a case of privilege escalation without requiring any…
-

Gamaredon Exploits WinRAR to Deliver GammaWorm and GammaSteel Against Ukraine [email protected] (The Hacker News)
The Russian hacking group known as Gamaredon has been attributed to the continued exploitation of a WinRAR vulnerability to deliver multiple malware families aimed at data theft and propagation. Per Sekoia, the activity involves the weaponization of CVE-2025-8088, a path traversal flaw in WinRAR, to launch an HTML Application payload dubbed GammaPhish, which is then…
-

Oracle WebLogic CVE-2024-21182 Added to KEV Catalog After Active Exploitation [email protected] (The Hacker News)
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a high-severity security flaw impacting Oracle WebLogic Server to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. The vulnerability, CVE-2024-21182 (CVSS score: 7.5), allows an unauthenticated attacker with network access to take control of susceptible servers. It wasRead More
-

AI-Driven Exploitation is Destroying Vulnerability Management. Here’s How to Handle It. [email protected] (The Hacker News)
AI-driven exploitation timelines are rapidly shrinking, and they are not going to stop shrinking. Vulnerabilities are being discovered, reproduced, and weaponized faster than ever in the history of enterprise security. As a result, the window between a vulnerability being disclosed and indiscriminate exploitation observed across the internet is now measured in hours, not days. The…
-
How to prepare security controls for future AI regulations
With so many competing compliance requirements related to AI, how could any CISO comply with all of them? Learn how to reconcile your AI strategy with the regulatory landscape.Read More
-

How Leading Organizations Are Turning EDR Into Operational Resilience [email protected] (The Hacker News)
Most organizations now recognize that endpoint protection alone is no longer sufficient. That’s why adoption of endpoint detection and response (EDR) has accelerated rapidly in recent years. Organizations understand that modern attacks move faster, evade traditional prevention controls, and require continuous visibility into suspicious activity across the environment. But owning EDRRead More
-

Pakistan-Linked SideCopy Targets Afghanistan Finance Ministry with Xeno RAT [email protected] (The Hacker News)
Cybersecurity researchers have disclosed details of a spear-phishing campaign likely undertaken by the Pakistan-aligned SideCopy group targeting Afghanistan’s Ministry of Finance with an open-source remote access trojan called Xeno RAT. “The campaign opens with a spear phishing delivery – a ZIP archive containing a malicious LNK file bearing a carefully crafted Pashto-language filename,”Read More
-
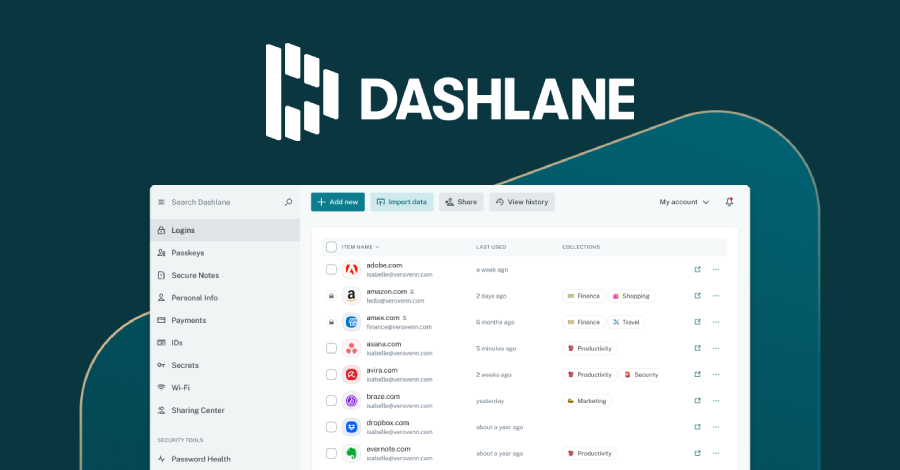
Dashlane Discloses Brute-Force Attack, Encrypted Vaults of Fewer Than 20 Users Downloaded [email protected] (The Hacker News)
Password manager Dashlane has disclosed that “fewer than” 20 users on the personal subscription plan had their encrypted vaults downloaded following a brute-force attack launched by an unknown party. On May 31, 2026, the company said an “external” threat actor launched a brute-force attack against certain Dashlane user accounts with the aim of breaking two-factor…
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
