“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-
Anatsa Android Banking Trojan Hits 90,000 Users with Fake PDF App on Google Play [email protected] (The Hacker News)
Cybersecurity researchers have discovered an Android banking malware campaign that has leveraged a trojan named Anatsa to target users in North America using malicious apps published on Google’s official app marketplace. The malware, disguised as a “PDF Update” to a document viewer app, has been caught serving a deceptive overlay when users attempt to access…
-
Malicious Pull Request Targets 6,000+ Developers via Vulnerable Ethcode VS Code Extension [email protected] (The Hacker News)
Cybersecurity researchers have flagged a supply chain attack targeting a Microsoft Visual Studio Code (VS Code) extension called Ethcode that has been installed a little over 6,000 times. The compromise, per ReversingLabs, occurred via a GitHub pull request that was opened by a user named Airez299 on June 17, 2025. First released by 7finney in…
-
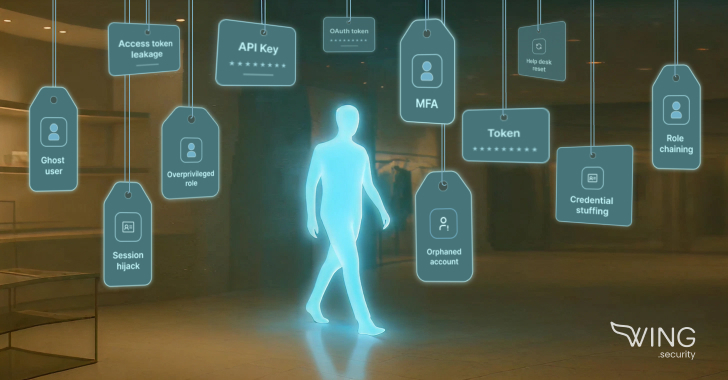
5 Ways Identity-based Attacks Are Breaching Retail [email protected] (The Hacker News)
From overprivileged admin roles to long-forgotten vendor tokens, these attackers are slipping through the cracks of trust and access. Here’s how five retail breaches unfolded, and what they reveal about… In recent months, major retailers like Adidas, The North Face, Dior, Victoria’s Secret, Cartier, Marks & Spencer, and Co‑op have all been breached. These attacks weren’t sophisticatedRead…
-

RondoDox Botnet Exploits Flaws in TBK DVRs and Four-Faith Routers to Launch DDoS Attacks [email protected] (The Hacker News)
Cybersecurity researchers are calling attention to a malware campaign that’s targeting security flaws in TBK digital video recorders (DVRs) and Four-Faith routers to rope the devices into a new botnet called RondoDox. The vulnerabilities in question include CVE-2024-3721, a medium-severity command injection vulnerability affecting TBK DVR-4104 and DVR-4216 DVRs, and CVE-2024-12856, an operatingRead More
-

BaitTrap: Over 17,000 Fake News Websites Caught Fueling Investment Fraud Globally [email protected] (The Hacker News)
A newly released report by cybersecurity firm CTM360 reveals a large-scale scam operation utilizing fake news websites—known as Baiting News Sites (BNS)—to deceive users into online investment fraud across 50 countries. These BNS pages are made to look like real news outlets: CNN, BBC, CNBC, or regional media. They publish fake stories that feature public…
-
What is the domain name system (DNS)?
The domain name system (DNS) is a naming database in which internet domain names are located and translated into Internet Protocol (IP) addresses.Read More
-
Phishing prevention: How to spot, stop and respond to scams
From email scams to BEC attacks, phishing is one of the biggest fish organizations must fry. Get advice on how to identify, prevent and respond to phishing schemes.Read More
-

Researchers Uncover Batavia Windows Spyware Stealing Documents from Russian Firms [email protected] (The Hacker News)
Russian organizations have been targeted as part of an ongoing campaign that delivers a previously undocumented Windows spyware called Batavia. The activity, per cybersecurity vendor Kaspersky, has been active since July 2024. “The targeted attack begins with bait emails containing malicious links, sent under the pretext of signing a contract,” the Russian company said. “The…
-
Researchers Uncover Batavia Windows Spyware Stealing Documents from Russian Firms [email protected] (The Hacker News)
Russian organizations have been targeted as part of an ongoing campaign that delivers a previously undocumented Windows spyware called Batavia. The activity, per cybersecurity vendor Kaspersky, has been active since July 2024. “The targeted attack begins with bait emails containing malicious links, sent under the pretext of signing a contract,” the Russian company said. “The…
-

CISA Adds Four Critical Vulnerabilities to KEV Catalog Due to Active Exploitation [email protected] (The Hacker News)
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added four security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The list of flaws is as follows – CVE-2014-3931 (CVSS score: 9.8) – A buffer overflow vulnerability in Multi-Router Looking Glass (MRLG) that could allow remote…
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
