“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-
Phishing prevention: How to spot, stop and respond to scams
From email scams to BEC attacks, phishing is one of the biggest fish organizations must fry. Get advice on how to identify, prevent and respond to phishing schemes.Read More
-

Researchers Uncover Batavia Windows Spyware Stealing Documents from Russian Firms [email protected] (The Hacker News)
Russian organizations have been targeted as part of an ongoing campaign that delivers a previously undocumented Windows spyware called Batavia. The activity, per cybersecurity vendor Kaspersky, has been active since July 2024. “The targeted attack begins with bait emails containing malicious links, sent under the pretext of signing a contract,” the Russian company said. “The…
-
Researchers Uncover Batavia Windows Spyware Stealing Documents from Russian Firms [email protected] (The Hacker News)
Russian organizations have been targeted as part of an ongoing campaign that delivers a previously undocumented Windows spyware called Batavia. The activity, per cybersecurity vendor Kaspersky, has been active since July 2024. “The targeted attack begins with bait emails containing malicious links, sent under the pretext of signing a contract,” the Russian company said. “The…
-

CISA Adds Four Critical Vulnerabilities to KEV Catalog Due to Active Exploitation [email protected] (The Hacker News)
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added four security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The list of flaws is as follows – CVE-2014-3931 (CVSS score: 9.8) – A buffer overflow vulnerability in Multi-Router Looking Glass (MRLG) that could allow remote…
-
How to implement zero trust: 7 expert steps
Zero trust means a lot more than determining how users access resources. Successful implementation takes time, commitment and ongoing support.Read More
-
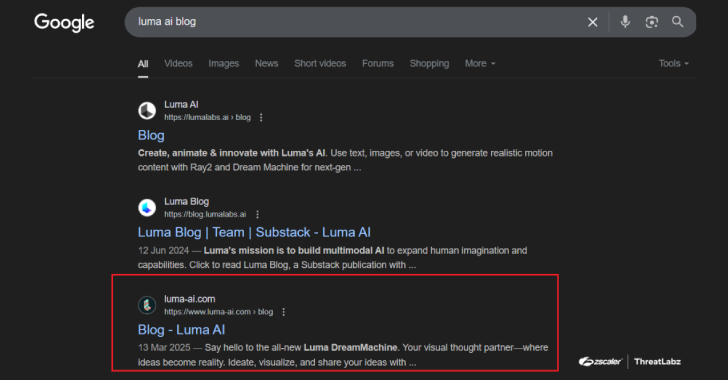
SEO Poisoning Campaign Targets 8,500+ SMB Users with Malware Disguised as AI Tools [email protected] (The Hacker News)
Cybersecurity researchers have disclosed a malicious campaign that leverages search engine optimization (SEO) poisoning techniques to deliver a known malware loader called Oyster (aka Broomstick or CleanUpLoader). The malvertising activity, per Arctic Wolf, promotes fake websites hosting trojanized versions of legitimate tools like PuTTY and WinSCP, aiming to trick software professionalsRead More
-
How to detect and fix a jailbroken iPhone
Jailbroken devices can give rise to security threats for users and organizations alike. Learn how to prevent, detect and remove jailbreaking on enterprise iPhones.Read More
-
The cloud’s role in PQC migration
Even though Q-Day might be several years away, enterprises should develop a strategic plan to prepare for the future. Experts share what challenges lie ahead with PQC migration.Read More
-
⚡ Weekly Recap: Chrome 0-Day, Ivanti Exploits, MacOS Stealers, Crypto Heists and More [email protected] (The Hacker News)
Everything feels secure—until one small thing slips through. Even strong systems can break if a simple check is missed or a trusted tool is misused. Most threats don’t start with alarms—they sneak in through the little things we overlook. A tiny bug, a reused password, a quiet connection—that’s all it takes. Staying safe isn’t just…
-
Manufacturing Security: Why Default Passwords Must Go [email protected] (The Hacker News)
If you didn’t hear about Iranian hackers breaching US water facilities, it’s because they only managed to control a single pressure station serving 7,000 people. What made this attack noteworthy wasn’t its scale, but how easily the hackers gained access — by simply using the manufacturer’s default password “1111.” This narrow escape prompted CISA to urge manufacturers…
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
