“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-
The cloud’s role in PQC migration
Even though Q-Day might be several years away, enterprises should develop a strategic plan to prepare for the future. Experts share what challenges lie ahead with PQC migration.Read More
-
⚡ Weekly Recap: Chrome 0-Day, Ivanti Exploits, MacOS Stealers, Crypto Heists and More [email protected] (The Hacker News)
Everything feels secure—until one small thing slips through. Even strong systems can break if a simple check is missed or a trusted tool is misused. Most threats don’t start with alarms—they sneak in through the little things we overlook. A tiny bug, a reused password, a quiet connection—that’s all it takes. Staying safe isn’t just…
-
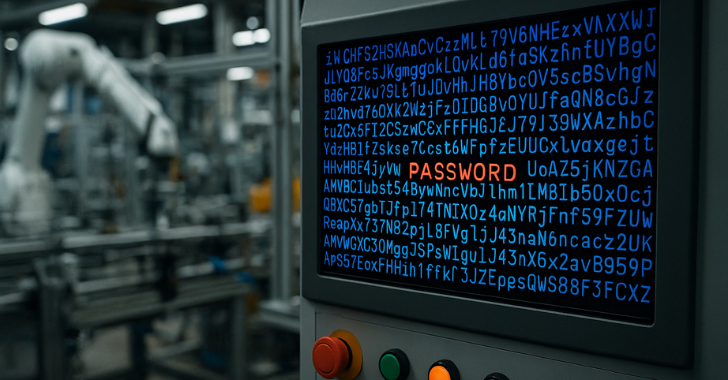
Manufacturing Security: Why Default Passwords Must Go [email protected] (The Hacker News)
If you didn’t hear about Iranian hackers breaching US water facilities, it’s because they only managed to control a single pressure station serving 7,000 people. What made this attack noteworthy wasn’t its scale, but how easily the hackers gained access — by simply using the manufacturer’s default password “1111.” This narrow escape prompted CISA to urge manufacturers…
-
TAG-140 Deploys DRAT V2 RAT, Targeting Indian Government, Defense, and Rail Sectors [email protected] (The Hacker News)
A hacking group with ties other than Pakistan has been found targeting Indian government organizations with a modified variant of a remote access trojan (RAT) called DRAT. The activity has been attributed by Recorded Future’s Insikt Group to a threat actor tracked as TAG-140, which it said overlaps with SideCopy, an adversarial collective assessed to…
-
What is the future of cybersecurity?
As cyberthreats grow more sophisticated, enterprises face mounting challenges. What does the future of cybersecurity hold, and how can organizations stay ahead?Read More
-
12 top enterprise risk management trends in 2025
Trends reshaping risk management include use of GRC platforms, risk maturity models, risk appetite statements and AI tools, plus the need to manage AI risks.Read More
-
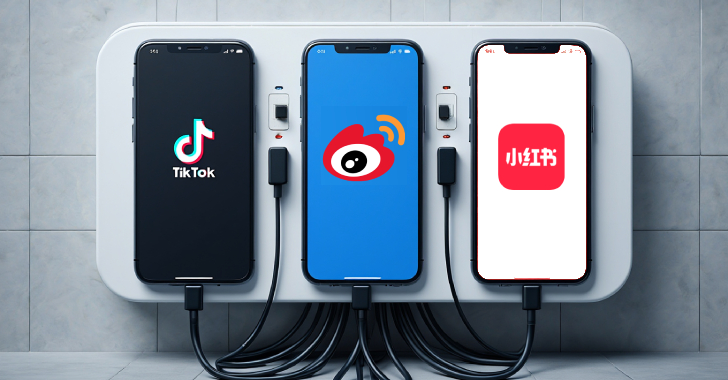
Taiwan NSB Alerts Public on Data Risks from TikTok, Weibo, and RedNote Over China Ties [email protected] (The Hacker News)
Taiwan’s National Security Bureau (NSB) has warned that China-developed applications like RedNote (aka Xiaohongshu), Weibo, TikTok, WeChat, and Baidu Cloud pose security risks due to excessive data collection and data transfer to China. The alert comes following an inspection of these apps carried out in coordination with the Ministry of Justice Investigation Bureau (MJIB) and…
-

Alert: Exposed JDWP Interfaces Lead to Crypto Mining, Hpingbot Targets SSH for DDoS [email protected] (The Hacker News)
Threat actors are weaponizing exposed Java Debug Wire Protocol (JDWP) interfaces to obtain code execution capabilities and deploy cryptocurrency miners on compromised hosts. “The attacker used a modified version of XMRig with a hard-“coded configuration, allowing them to avoid suspicious command-line arguments that are often flagged by defenders,” Wiz researchers Yaara Shriki and GiliRead More
-
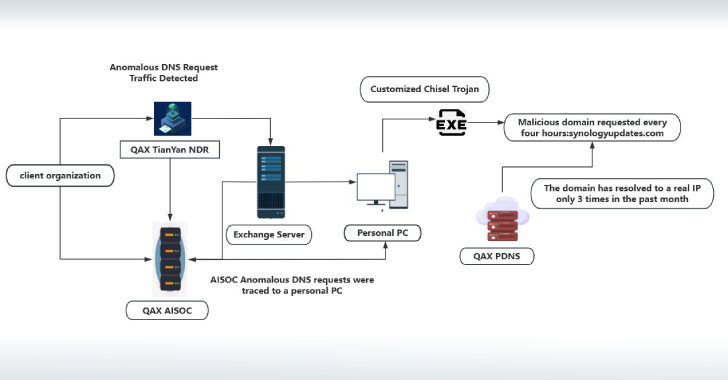
NightEagle APT Exploits Microsoft Exchange Flaw to Target China’s Military and Tech Sectors [email protected] (The Hacker News)
Cybersecurity researchers have shed light on a previously undocumented threat actor called NightEagle (aka APT-Q-95) that has been observed targeting Microsoft Exchange servers as a part of a zero-day exploit chain designed to target government, defense, and technology sectors in China. According to QiAnXin’s RedDrip Team, the threat actor has been active since 2023 and…
-

Your AI Agents Might Be Leaking Data — Watch this Webinar to Learn How to Stop It [email protected] (The Hacker News)
Generative AI is changing how businesses work, learn, and innovate. But beneath the surface, something dangerous is happening. AI agents and custom GenAI workflows are creating new, hidden ways for sensitive enterprise data to leak—and most teams don’t even realize it. If you’re building, deploying, or managing AI systems, now is the time to ask:…
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
