“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-
Tips to find cyber insurance coverage in 2025
Most businesses have a form of cyber insurance, either through cyber liability and data breach endorsements in traditional business policies or through standalone cyber policies.Read More
-
Experts Uncover Four New Privilege Escalation Flaws in Windows Task Scheduler [email protected] (The Hacker News)
Cybersecurity researchers have detailed four different vulnerabilities in a core component of the Windows task scheduling service that could be exploited by local attackers to achieve privilege escalation and erase logs to cover up evidence of malicious activities. The issues have been uncovered in a binary named “schtasks.exe,” which enables an administrator to create, delete,…
-
What is Pretty Good Privacy and how does it work?
Pretty Good Privacy, or PGP, was a popular program used to encrypt and decrypt email over the internet, as well as authenticate messages with digital signatures and encrypted stored files.Read More
-

Google Blocked 5.1B Harmful Ads and Suspended 39.2M Advertiser Accounts in 2024 [email protected] (The Hacker News)
Google on Wednesday revealed that it suspended over 39.2 million advertiser accounts in 2024, with a majority of them identified and blocked by its systems before it could serve harmful ads to users. In all, the tech giant said it stopped 5.1 billion bad ads, restricted 9.1 billion ads, and blocked or restricted ads on…
-

Gamma AI Platform Abused in Phishing Chain to Spoof Microsoft SharePoint Logins [email protected] (The Hacker News)
Threat actors are leveraging an artificial intelligence (AI) powered presentation platform named Gamma in phishing attacks to direct unsuspecting users to spoofed Microsoft login pages. “Attackers weaponize Gamma, a relatively new AI-based presentation tool, to deliver a link to a fraudulent Microsoft SharePoint login portal,” Abnormal Security researchers Hinman Baron and Piotr Wojtyla said inRead…
-

From Third-Party Vendors to U.S. Tariffs: The New Cyber Risks Facing Supply Chains [email protected] (The Hacker News)
Introduction Cyber threats targeting supply chains have become a growing concern for businesses across industries. As companies continue to expand their reliance on third-party vendors, cloud-based services, and global logistics networks, cybercriminals are exploiting vulnerabilities within these interconnected systems to launch attacks. By first infiltrating a third-party vendor with undetectedRead More
-

New BPFDoor Controller Enables Stealthy Lateral Movement in Linux Server Attacks [email protected] (The Hacker News)
Cybersecurity researchers have unearthed a new controller component associated with a known backdoor called BPFDoor as part of cyber attacks targeting telecommunications, finance, and retail sectors in South Korea, Hong Kong, Myanmar, Malaysia, and Egypt in 2024. “The controller could open a reverse shell,” Trend Micro researcher Fernando Mercês said in a technical report published…
-
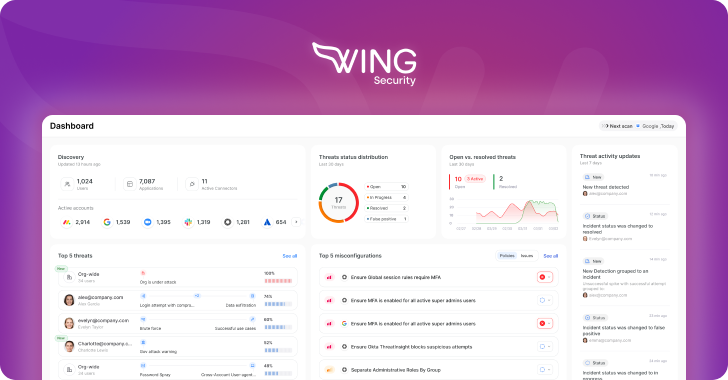
Product Walkthrough: A Look Inside Wing Security’s Layered SaaS Identity Defense [email protected] (The Hacker News)
Intro: Why hack in when you can log in? SaaS applications are the backbone of modern organizations, powering productivity and operational efficiency. But every new app introduces critical security risks through app integrations and multiple users, creating easy access points for threat actors. As a result, SaaS breaches have increased, and according to a May…
-
Chinese Android Phones Shipped with Fake WhatsApp, Telegram Apps Targeting Crypto Users [email protected] (The Hacker News)
Cheap Android smartphones manufactured by Chinese companies have been observed pre-installed with trojanized apps masquerading as WhatsApp and Telegram that contain cryptocurrency clipper functionality as part of a campaign since June 2024. While using malware-laced apps to steal financial information is not a new phenomenon, the new findings from Russian antivirus vendor Doctor Web point…
-

U.S. Govt. Funding for MITRE’s CVE Ends April 16, Cybersecurity Community on Alert [email protected] (The Hacker News)
The U.S. government funding for non-profit research giant MITRE to operate and maintain its Common Vulnerabilities and Exposures (CVE) program will expire Wednesday, an unprecedented development that could shake up one of the foundational pillars of the global cybersecurity ecosystem. The 25-year-old CVE program is a valuable tool for vulnerability management, offering a de facto…
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
