“Cyber warfare is as much about psychological strategy as technical prowess.”
― James Scott
-

North Korean Hackers Target Web3 with Nim Malware and Use ClickFix in BabyShark Campaign [email protected] (The Hacker News)
Threat actors with ties to North Korea have been observed targeting Web3 and cryptocurrency-related businesses with malware written in the Nim programming language, underscoring a constant evolution of their tactics. “Unusually for macOS malware, the threat actors employ a process injection technique and remote communications via wss, the TLS-encrypted version of the WebSocket protocol,”Read More
-
What is a message authentication code (MAC)? How it works and best practices
A message authentication code (MAC) is a cryptographic checksum applied to a message to guarantee its integrity and authenticity.Read More
-

That Network Traffic Looks Legit, But it Could be Hiding a Serious Threat [email protected] (The Hacker News)
With nearly 80% of cyber threats now mimicking legitimate user behavior, how are top SOCs determining what’s legitimate traffic and what is potentially dangerous? Where do you turn when firewalls and endpoint detection and response (EDR) fall short at detecting the most important threats to your organization? Breaches at edge devices and VPN gateways have…
-

Hackers Using PDFs to Impersonate Microsoft, DocuSign, and More in Callback Phishing Campaigns [email protected] (The Hacker News)
Cybersecurity researchers are calling attention to phishing campaigns that impersonate popular brands and trick targets into calling phone numbers operated by threat actors. “A significant portion of email threats with PDF payloads persuade victims to call adversary-controlled phone numbers, displaying another popular social engineering technique known as Telephone-Oriented Attack Delivery (TOADRead More
-
What is business continuity software?
Business continuity software is an application or suite designed to make business continuity planning/business continuity management (BCP/BCM) processes, metrics and compliance more efficient and accurate.Read More
-
What is the principle of least privilege (POLP)?
The principle of least privilege (POLP) is a concept in computer security that limits users’ access rights to only what is strictly required to do their jobs.Read More
-
What is SIEM (security information and event management)?
SIEM (security information and event management) is software that helps organizations detect, analyze, and respond to security threats by collecting and correlating security event data from across the IT environment in real time.Read More
-
What is quantum key distribution (QKD)?
Quantum key distribution (QKD) is a secure communication method for exchanging encryption keys only known between shared parties.Read More
-

U.S. Sanctions Russian Bulletproof Hosting Provider for Supporting Cybercriminals Behind Ransomware [email protected] (The Hacker News)
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has levied sanctions against Russia-based bulletproof hosting (BPH) service provider Aeza Group to assist threat actors in their malicious activities and targeting victims in the country and across the world. The sanctions also extend to its subsidiaries Aeza International Ltd., the U.K. branch…
-
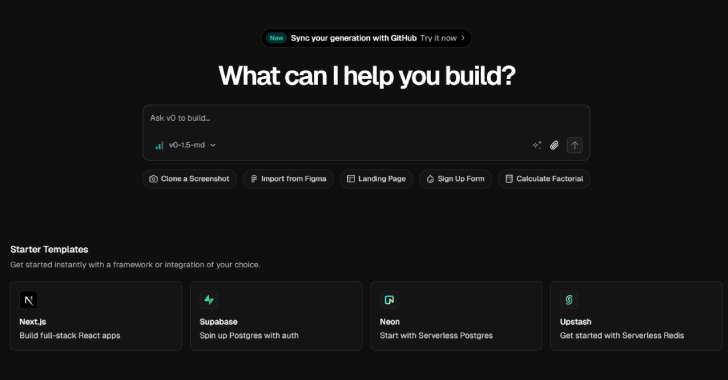
Vercel’s v0 AI Tool Weaponized by Cybercriminals to Rapidly Create Fake Login Pages at Scale [email protected] (The Hacker News)
Unknown threat actors have been observed weaponizing v0, a generative artificial intelligence (AI) tool from Vercel, to design fake sign-in pages that impersonate their legitimate counterparts. “This observation signals a new evolution in the weaponization of Generative AI by threat actors who have demonstrated an ability to generate a functional phishing site from simple text…
“Security used to be an inconvenience sometimes, but now it’s a necessity all the time.”
― Martina Navratilova
